How to install and use CSF on OpenSUSE leap 42.1
To Install and Use CSF on OpenSUSE leap 42.1
Config Server Firewall is abbreviated as CSF. CSf is the most commonly using firewall application to secure Linux servers. CSF has wide range of options to manage Linux firewall via comman-line and from the control panel. The csf installation includes preconfigured configurations and control panel UI’ s for cPanel, DirectAdmin and Webmin.This article covers the method to install CSF on OpenSUSE leap 42.1.
Installing CSF
Before you begin with the process, you need to move to the directory where you want to download the package. Run the following command for the same purpose.
linuxhelp:~ # cd /usr/src/
Next, downlaod CSF using wget command in the following manner.
linuxhelp:/usr/src # wget https://download.configserver.com/csf.tgz
--2017-11-16 12:56:02-- https://download.configserver.com/csf.tgz
Resolving download.configserver.com (download.configserver.com)... 85.10.199.177
Connecting to download.configserver.com (download.configserver.com)|85.10.199.177|:443... connected.
HTTP request sent, awaiting response... 200 OK
Length: 1546204 (1.5M) [application/x-gzip]
Saving to: ‘ csf.tgz’
100%[=================================================================================================> ] 1,546,204 22.2KB/s in 64s
2017-11-16 12:57:07 (23.6 KB/s) - ‘ csf.tgz’ saved [1546204/1546204]
After that, you need to extract the package by running the following command.
linuxhelp:/usr/src # tar -xzf csf.tgz
Then, move inside the extracted directory by making use of the following command.
linuxhelp:/usr/src # cd csf/
Here, you can install CSF by executing the below mentioned command.
linuxhelp:/usr/src/csf # sh install.sh
Selecting installer...
Running csf generic installer
Installing generic csf and lfd
Check we' re running as root
Checking Perl modules...
Configuration modified for SuSE settings /etc/csf/csf.conf
...Perl modules OK
mkdir: created directory ‘ /etc/csf’
.
.
.
.
‘ csf/configserver.css’ -> ‘ webmin/csf/images/configserver.css’
‘ csf/csf-loader.gif’ -> ‘ webmin/csf/images/csf-loader.gif’
‘ csf/csf.svg’ -> ‘ webmin/csf/images/csf.svg’
‘ csf/csf_small.png’ -> ‘ webmin/csf/images/csf_small.png’
‘ csf/jquery.min.js’ -> ‘ webmin/csf/images/jquery.min.js’
‘ csf/loader.gif’ -> ‘ webmin/csf/images/loader.gif’
‘ /etc/csf/csfwebmin.tgz’ -> ‘ /usr/local/csf/csfwebmin.tgz’
Installation Completed
After the installation, you shall check if you have the required iptables modules. And for that, you need to run the following command.
linuxhelp:/usr/src/csf # perl /usr/local/csf/bin/csftest.pl
Testing ip_tables/iptable_filter...open3: exec of /sbin/iptables -I OUTPUT -p tcp --dport 9999 -j ACCEPT
CSF Configuration
We have installed the CSF in testing mode so it does not provide full protection of your server from attacks. For disabling the testing mode you should configure the CSF according to your requirement. So, open the configuration file.
linuxhelp:/usr/src/csf # vim /etc/csf/csf.conf
And change the testing mode by simply changing the variable of testing from TESTING = “ 1” to “ TESTING=0” .
# Allow incoming TCP ports TCP_IN =” 20,21,22,25,53,80,110,143,443,465,587,993,995” # Allow outgoing TCP ports TCP_OUT =” 20,21,22,25,53,80,110,113,443” # Allow incoming UDP ports UDP_IN = “ 20,21,53” # Allow incoming UDP ports # to allow traceroute add 33434:33523 to the list UDP_OUT =” 20,21,53,113,123”
Later, you shall start your csf service and check its status.
linuxhelp:/usr/src/csf # systemctl start csf linuxhelp:/usr/src/csf # systemctl status csf csf.service - ConfigServer Firewall & Security - csf Loaded: loaded (/usr/lib/systemd/system/csf.service enabled) Active: active (exited) since Thu 2017-11-16 13:04:54 IST 1s ago Process: 11434 ExecStart=/usr/sbin/csf --initup (code=exited, status=0/SUCCESS) Main PID: 11434 (code=exited, status=0/SUCCESS) Nov 16 13:04:54 linuxhelp csf[11434]: ACCEPT udp opt -- in !lo out * 8.8.4.4 -> 0.0.0.0/0 udp dpt:53 Nov 16 13:04:54 linuxhelp csf[11434]: ACCEPT tcp opt -- in !lo out * 8.8.4.4 -> 0.0.0.0/0 tcp dpt:53 Nov 16 13:04:54 linuxhelp csf[11434]: ACCEPT udp opt -- in * out !lo 0.0.0.0/0 -> 8.8.4.4 udp spt:53 Nov 16 13:04:54 linuxhelp csf[11434]: ACCEPT tcp opt -- in * out !lo 0.0.0.0/0 -> 8.8.4.4 tcp spt:53 Nov 16 13:04:54 linuxhelp csf[11434]: ACCEPT udp opt -- in * out !lo 0.0.0.0/0 -> 8.8.4.4 udp dpt:53 Nov 16 13:04:54 linuxhelp csf[11434]: ACCEPT tcp opt -- in * out !lo 0.0.0.0/0 -> 8.8.4.4 tcp dpt:53 Nov 16 13:04:54 linuxhelp csf[11434]: LOCALOUTPUT all opt -- in * out !lo 0.0.0.0/0 -> 0.0.0.0/0 Nov 16 13:04:54 linuxhelp csf[11434]: LOCALINPUT all opt -- in !lo out * 0.0.0.0/0 -> 0.0.0.0/0 Nov 16 13:04:54 linuxhelp csf[11434]: *WARNING* TESTING mode is enabled - do not forget to disable it in the configuration Nov 16 13:04:54 linuxhelp systemd[1]: Started ConfigServer Firewall & Security - csf.
Options in CSF
If you want to allow an IP, you shall run the -a option followed by the IP.
linuxhelp:/usr/src/csf # csf -a 192.168.7.219
Adding 192.168.7.219 to csf.allow only while in TESTING mode (not iptables ACCEPT)
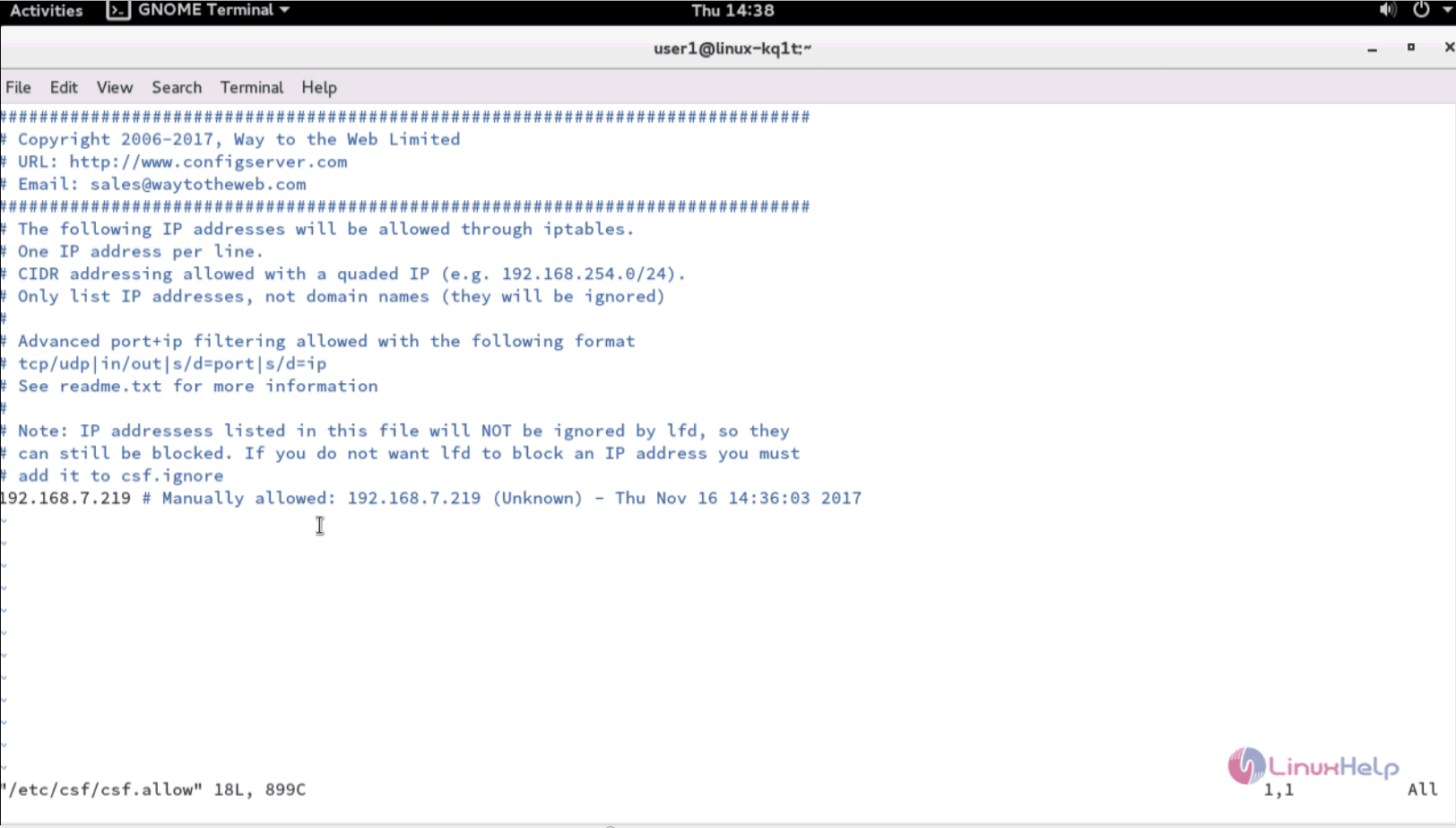
Next, open your csf.allow file
linuxhelp:/usr/src/csf # vim /etc/csf/csf.allow
You' ll see the IP that was added.
192.168.7.219 # Manually allowed: 192.168.7.219 (Unknown) - Thu Nov 16 13:06:58 2017
You shall remove that IP from your allow list by using the -ar option along with the IP.
linuxhelp:/usr/src/csf # csf -ar 192.168.7.219
Removing rule...
iptables: Bad rule (does a matching rule exist in that chain?).
ACCEPT all opt -- in !lo out * 192.168.7.219 -> 0.0.0.0/0
iptables: Bad rule (does a matching rule exist in that chain?).
ACCEPT all opt -- in * out !lo 0.0.0.0/0 -> 192.168.7.219
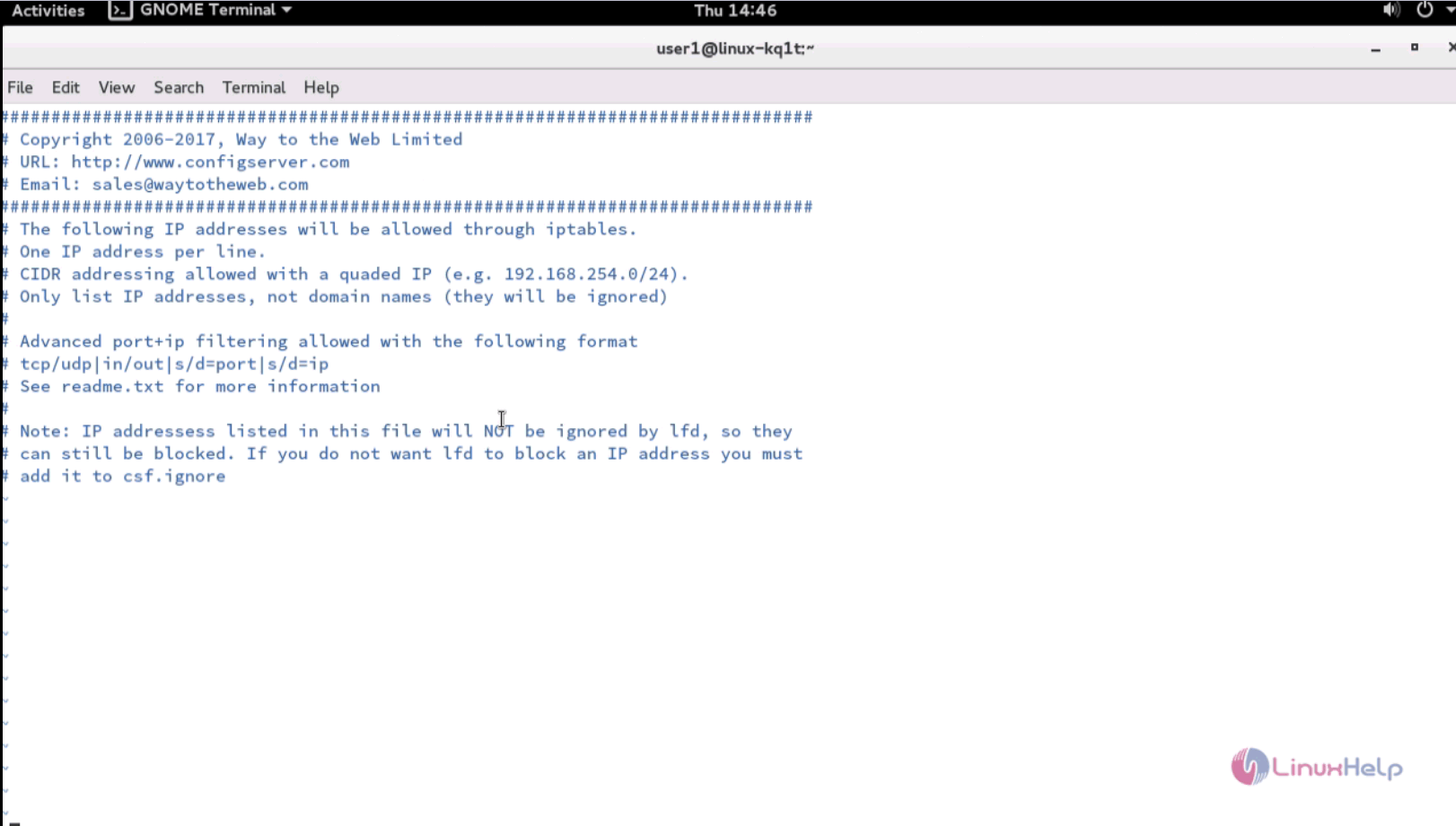
You shall also check if it is removed.
linuxhelp:/usr/src/csf # vim /etc/csf/csf.allow
If you want to deny the IP address, you shall simply use the -d option in the following manner.
linuxhelp:/usr/src/csf # csf -d 192.168.7.219
Adding 192.168.7.219 to csf.deny and iptables DROP...
iptables: No chain/target/match by that name.
DROP all opt -- in !lo out * 192.168.7.219 -> 0.0.0.0/0
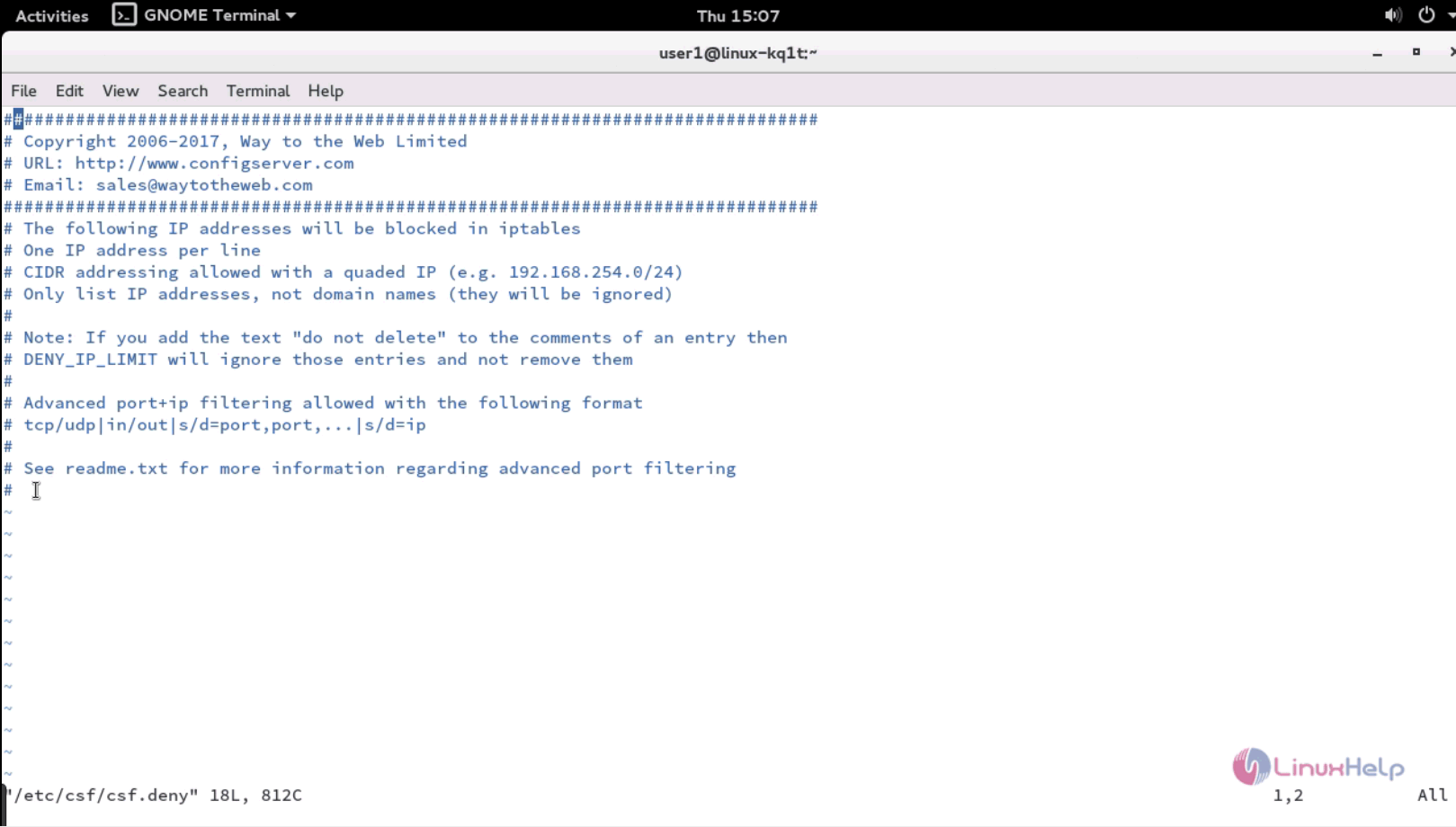
You can check if the denied IP is added in the csf.deny file.
linuxhelp:/usr/src/csf # vim /etc/csf/csf.deny
192.168.7.219 # Manually denied: 192.168.7.219 (Unknown) - Thu Nov 16 13:11:24 2017
You can remove the denied IP from the csf.deny file by running the dr option.
linuxhelp:/usr/src/csf # csf -dr 192.168.7.219
Removing rule...
DROP all opt -- in !lo out * 192.168.7.219 -> 0.0.0.0/0
LOGDROPOUT all opt -- in * out !lo 0.0.0.0/0 -> 192.168.7.219
You can check and see the csf.deny file.
You can grep the IP address by running the -g option.
linuxhelp:/usr/src/csf # csf -g 192.168.7.219
Chain num pkts bytes target prot opt in out source destination
DENYIN 1 0 0 DROP all -- !lo * 192.168.7.219 0.0.0.0/0
DENYOUT 1 0 0 LOGDROPOUT all -- * !lo 0.0.0.0/0 192.168.7.219
csf.deny: 192.168.7.219 # Manually denied: 192.168.7.219 (Unknown) - Thu Nov 16 13:11:24 2017
You can also completly disable csf by using the x option.
linuxhelp:/usr/src/csf # csf -x
Flushing chain `INPUT'
Flushing chain `FORWARD'
Flushing chain `OUTPUT'
Flushing chain `PREROUTING'
Flushing chain `INPUT'
Flushing chain `OUTPUT'
Flushing chain `POSTROUTING'
csf and lfd have been disabled
You can enable the disabled CSF by using the -e option.
linuxhelp:/usr/src/csf # csf -e
DROP tcp opt -- in * out * 0.0.0.0/0 -> 0.0.0.0/0 tcp dpt:23
DROP udp opt -- in * out * 0.0.0.0/0 -> 0.0.0.0/0 udp dpt:23
DROP tcp opt -- in * out * 0.0.0.0/0 -> 0.0.0.0/0 tcp dpt:67
DROP udp opt -- in * out * 0.0.0.0/0 -> 0.0.0.0/0 udp dpt:67
DROP tcp opt -- in * out * 0.0.0.0/0 -> 0.0.0.0/0 tcp dpt:68
DROP udp opt -- in * out * 0.0.0.0/0 -> 0.0.0.0/0 udp dpt:68
DROP tcp opt -- in * out * 0.0.0.0/0 -> 0.0.0.0/0 tcp dpt:111
.
.
.
.
lfd.service - ConfigServer Firewall & Security - lfd
Loaded: loaded (/usr/lib/systemd/system/lfd.service enabled)
Active: active (running) since Thu 2017-11-16 13:14:37 IST 9ms ago
Process: 11993 ExecStart=/usr/sbin/lfd (code=exited, status=0/SUCCESS)
Main PID: 12001 (lfd - starting)
CGroup: /system.slice/lfd.service
└─12001 lfd - starting
Nov 16 13:14:36 linuxhelp systemd[1]: Starting ConfigServer Firewall & Security - lfd...
Nov 16 13:14:37 linuxhelp systemd[1]: Started ConfigServer Firewall & Security - lfd.
csf and lfd have been enabled
If you want to check the IPv4 iptables configuration run the -l option.
linuxhelp:/usr/src/csf # csf -l
Chain INPUT (policy DROP 0 packets, 0 bytes)
num pkts bytes target prot opt in out source destination
1 0 0 ACCEPT tcp -- !lo * 8.8.4.4 0.0.0.0/0 tcp dpt:53
2 0 0 ACCEPT udp -- !lo * 8.8.4.4 0.0.0.0/0 udp dpt:53
3 0 0 ACCEPT tcp -- !lo * 8.8.4.4 0.0.0.0/0 tcp spt:53
4 0 0 ACCEPT udp -- !lo * 8.8.4.4 0.0.0.0/0 udp spt:53
Chain PREROUTING (policy ACCEPT 7 packets, 697 bytes)
num pkts bytes target prot opt in out source destination
Chain INPUT (policy ACCEPT 3 packets, 234 bytes)
num pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 8 packets, 519 bytes)
num pkts bytes target prot opt in out source destination
Chain POSTROUTING (policy ACCEPT 8 packets, 519 bytes)
num pkts bytes target prot opt in out source destination
You can start the csf service with the -s command.
linuxhelp:/usr/src/csf # csf -s
Flushing chain `INPUT'
Flushing chain `FORWARD'
Flushing chain `OUTPUT'
Flushing chain `ALLOWIN'
Flushing chain `ALLOWOUT'
Flushing chain `DENYIN'
Flushing chain `DENYOUT'
ACCEPT udp opt -- in * out !lo 0.0.0.0/0 -> 8.8.4.4 udp spt:53
ACCEPT tcp opt -- in * out !lo 0.0.0.0/0 -> 8.8.4.4 tcp spt:53
ACCEPT udp opt -- in * out !lo 0.0.0.0/0 -> 8.8.4.4 udp dpt:53
ACCEPT tcp opt -- in * out !lo 0.0.0.0/0 -> 8.8.4.4 tcp dpt:53
LOCALOUTPUT all opt -- in * out !lo 0.0.0.0/0 -> 0.0.0.0/0
LOCALINPUT all opt -- in !lo out * 0.0.0.0/0 -> 0.0.0.0/0
You shall restart the csf service by running the command with the -r option.
linuxhelp:/usr/src/csf # csf -r
Flushing chain `INPUT'
Flushing chain `FORWARD'
Flushing chain `OUTPUT'
Flushing chain `ALLOWIN'
Flushing chain `ALLOWOUT'
Flushing chain `DENYIN'
Flushing chain `DENYOUT'
ACCEPT udp opt -- in * out !lo 0.0.0.0/0 -> 8.8.4.4 udp spt:53
ACCEPT tcp opt -- in * out !lo 0.0.0.0/0 -> 8.8.4.4 tcp spt:53
ACCEPT udp opt -- in * out !lo 0.0.0.0/0 -> 8.8.4.4 udp dpt:53
ACCEPT tcp opt -- in * out !lo 0.0.0.0/0 -> 8.8.4.4 tcp dpt:53
LOCALOUTPUT all opt -- in * out !lo 0.0.0.0/0 -> 0.0.0.0/0
LOCALINPUT all opt -- in !lo out * 0.0.0.0/0 -> 0.0.0.0/0
With this, the installation and usage of CSF comes to an end.
Comments ( 0 )
No comments available